
Extract Data instantly from any website in minutes without coding using our ready made extractors
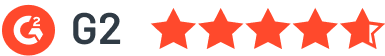
Built for continuous data collection , zero maintenance

Easily select the sources that matter most to you, from a vast range of websites and datasets
Tailor your data extraction by setting your preferences, and let our tool do the heavy lifting by extracting the structured data you need

Seamlessly download your data or integrate it directly into your workflow with support for multiple formats (CSV, Excel, JSON, JSONL, XML) and platforms
Get our concierge to build an extractor for you.
Enter URL, Select elements and submit.
We will build one for you to run on WebAutomation.
Let's Build One For Free
The file sat heavy on the desktop: .
He closed the browser at midnight, but left the zip on his desktop. Not a tool anymore. A memento. A promise that understanding the cracks in the system was the first step to defending it.
Within minutes, the DVWA splash screen glowed on his browser. Low security. Medium. High. Impossible. Each level a riddle wrapped in an exploit. SQL injection, command execution, XSS—they were all there, sleeping inside the code like traps waiting to be tested.
"Let’s see what trouble we can find tonight," he muttered, firing up XAMPP.
But tonight wasn’t about checking boxes. It was about the story behind the zip. A friend had sent it with a cryptic message: “Found this on an old drive from that bootcamp. Remember the night we broke the admin panel?”
He started simple. A ' OR '1'='1 in the user ID field. Boom. The database spilled its test credentials like a confession. Too easy. He moved to file inclusion, then to upload vulnerabilities, each success sharpening his instincts.
Alex smiled. That bootcamp had changed everything. They weren’t just students then—they were hunters learning the dark corners of the web so they could patch them. DVWA was their first great teacher, forgiving enough for beginners, deep enough to keep you up until 3 a.m.
To anyone else, it might look like a simple archive—maybe old homework, maybe a forgotten backup. But Alex knew better. Damn Vulnerable Web Application wasn’t just a tool; it was a digital shooting range where security researchers like him learned to think like attackers before the real ones struck.
He double-clicked. The zip unfolded into a folder of PHP scripts, config files, and a familiar login screen waiting to be spun up on localhost.
Somewhere, on a server far away, a real vulnerability waited. But tonight, in the quiet glow of localhost, Alex was home.
Tired of getting blocked while web scraping? Our powerful infrastructure that runs on the cloud takes care of everything so you focus on getting the data you need, when you need it.

No coding required. Processes like retries, scheduling and integrations are automated allowing for minimal user intervention

Our architecture makes webautomation.io resilient to failures using rotation of a large pool of proxies and browser fingerprinting technology

Our engineers are consistently monitoring and fixing code as the sources change. Allowing infinite scalability without service interruptions
Tired of getting blocked while web scraping? Our powerful infrastructure that runs on the cloud takes care of everything so you focus on getting the data you need, when you need it.
The file sat heavy on the desktop: .
He closed the browser at midnight, but left the zip on his desktop. Not a tool anymore. A memento. A promise that understanding the cracks in the system was the first step to defending it.
Within minutes, the DVWA splash screen glowed on his browser. Low security. Medium. High. Impossible. Each level a riddle wrapped in an exploit. SQL injection, command execution, XSS—they were all there, sleeping inside the code like traps waiting to be tested.
"Let’s see what trouble we can find tonight," he muttered, firing up XAMPP.
But tonight wasn’t about checking boxes. It was about the story behind the zip. A friend had sent it with a cryptic message: “Found this on an old drive from that bootcamp. Remember the night we broke the admin panel?”
He started simple. A ' OR '1'='1 in the user ID field. Boom. The database spilled its test credentials like a confession. Too easy. He moved to file inclusion, then to upload vulnerabilities, each success sharpening his instincts.
Alex smiled. That bootcamp had changed everything. They weren’t just students then—they were hunters learning the dark corners of the web so they could patch them. DVWA was their first great teacher, forgiving enough for beginners, deep enough to keep you up until 3 a.m.
To anyone else, it might look like a simple archive—maybe old homework, maybe a forgotten backup. But Alex knew better. Damn Vulnerable Web Application wasn’t just a tool; it was a digital shooting range where security researchers like him learned to think like attackers before the real ones struck.
He double-clicked. The zip unfolded into a folder of PHP scripts, config files, and a familiar login screen waiting to be spun up on localhost.
Somewhere, on a server far away, a real vulnerability waited. But tonight, in the quiet glow of localhost, Alex was home.
See how our clients are transforming their businesses with our powerful data extraction solutions.
Everything you need to know about the product and billing.
WebAutomation is a powerful web scraping platform that allows you to extract data from any website without coding. Simply choose from our pre-built extractors or create your own custom extractor. Our platform handles everything from IP rotation to CAPTCHA solving, ensuring reliable data extraction. dvwa master.zip
Yes, absolutely! Our platform is designed to be user-friendly and requires no coding knowledge. You can use our pre-built extractors or our visual selector tool to create custom extractors. Our intuitive interface guides you through the entire process. The file sat heavy on the desktop:
We take security seriously. All data extraction is done through secure connections, and we implement various security measures including IP rotation, user-agent rotation, and proxy support. Your data is encrypted in transit and at rest. A memento
Yes, we provide comprehensive support and training for new users. This includes detailed documentation, video tutorials, and dedicated support channels. We also offer personalized onboarding sessions to help you get started quickly.

Can't find the answer you're looking for? Please chat to our friendly team.
Join over 4,000+ businesses already growing with Web Automation.