3.0.0-alpha.2 Exploit - Pico
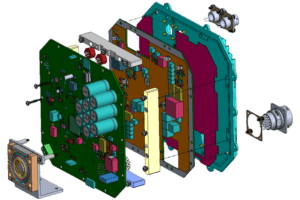
Maverick, an expert in low-level programming, took the lead, crafting a custom-made exploit that would fit into a mere 32 bytes of memory. The code was so elegant, so precise, that it seemed almost like a work of art.
The room was electric with tension as the team watched the target machine's screen flicker. The boot process, normally a smooth and uneventful sequence, began to stutter and hiccup. The kernel's memory protection mechanisms were breached, and the exploit began to inject a custom payload. Pico 3.0.0-alpha.2 Exploit
The exploit was responsibly disclosed to the Pico development team, who were initially stunned but ultimately impressed by the elegance and sophistication of the attack. The team behind Pico vowed to learn from their mistakes, and the cybersecurity community was once again reminded that even the most secure systems can be vulnerable. Maverick, an expert in low-level programming, took the
Lord Nexus, the group's strategist, carefully planned the attack. They would use a combination of social engineering and clever routing to get their exploit onto a target machine running Pico 3.0.0-alpha.2. The chosen victim was a high-profile researcher at a top cybersecurity firm, known for his work on operating system security. The boot process, normally a smooth and uneventful
The payload, designed by Lord Nexus, was a proof-of-concept (PoC) that would demonstrate the team's capabilities without causing any lasting harm. It simply displayed a message on the screen, a subtle nod to the researchers who had worked on Pico: "Your alpha.2 just got owned."